Cutting-Edge Cybersecurity Solutions
CYPENTA is committed to ensuring the integrity, confidentiality, and security of digital systems in an increasingly connected world.
About CYPENTA
We are a team of passionate innovators dedicated to solving complex security challenges. Our mission is to build trustworthy digital solutions for a better future.
Our Flagship Products
Digi-Ballot
A secure, accessible, and transparent digital voting platform designed to ensure the integrity and efficiency of elections.
LOCK
A hybrid security model that integrates physical intervention with digital security, making systems quantum-resistant and immune to remote hacks.
Meet the Team
The minds behind CYPENTA's innovative solutions.
Deepu C P
Lajin C P
Swathi Ravi M
Adithya Gopalakrishnan
Faheema Hassan
Get In Touch
We are always looking for feedback and partners. Reach out to us to learn more.
techcypenta@gmail.comDigi-Ballot
Empowering every voter in India with a secure, accessible, and transparent digital voting platform.
The Challenge with Current Elections
The traditional voting process faces several critical issues.
Electoral Fraud
Paper ballots and EVMs are vulnerable to tampering and fraudulent voting.
Low Voter Turnout
Long queues and inconvenience discourage participation.
Manual Processes
Manual counting is slow, inefficient, and prone to human error.
Storage & Security
Physical ballots and EVMs are at risk of damage or tampering.
Our Solution: Digi-Ballot
Digi-Ballot revolutionizes the voting process with four key pillars.
Biometric Authentication
Using Aadhaar-linked fingerprints to ensure authorized voting.
Remote Accessibility
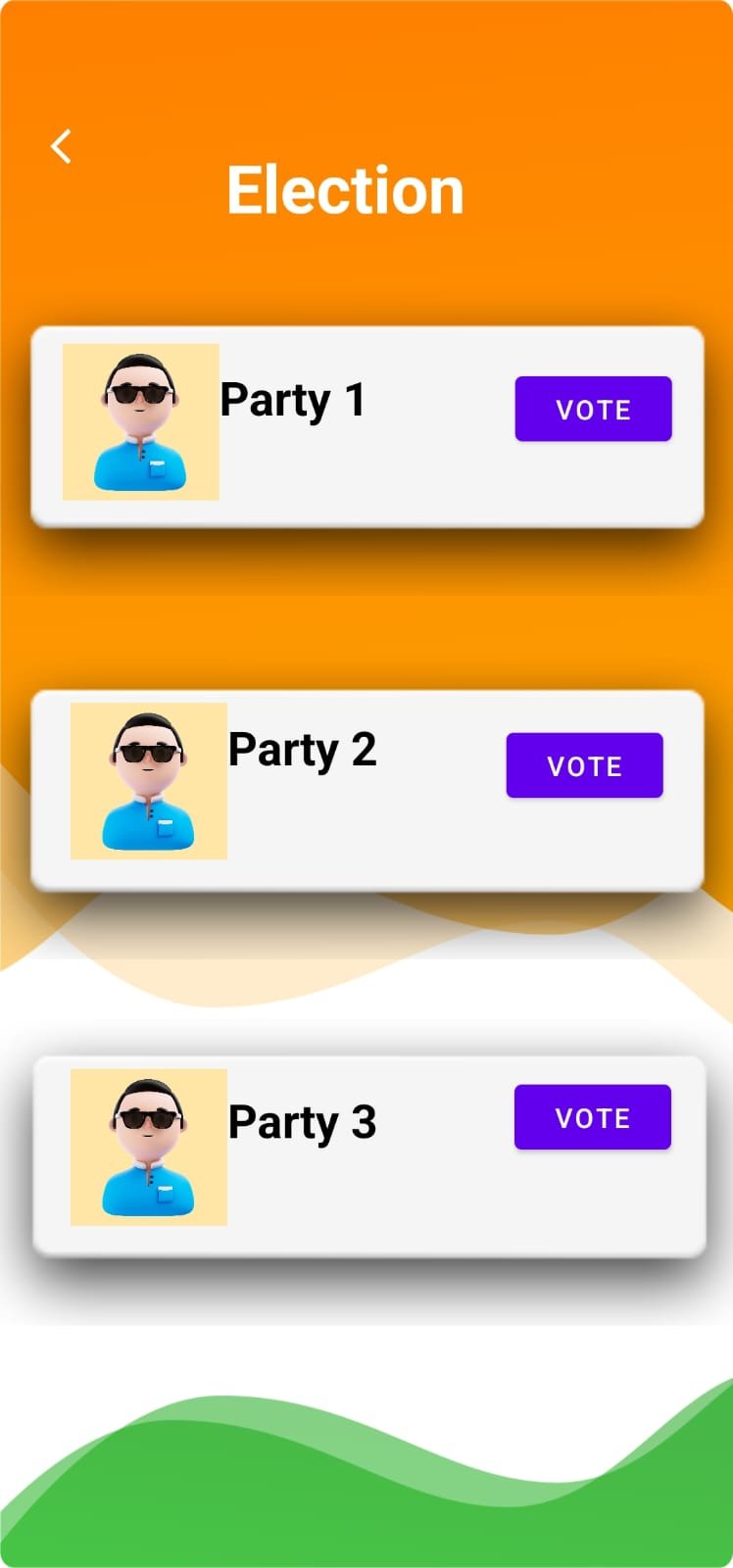
Cast your vote securely from any location using our mobile app.
Tamper-Proof Security
Multi-layer encryption and data verification guarantee vote integrity.
Instant Results
Automated system for real-time, authenticated results.
App Features
A user-friendly experience from registration to casting your vote.

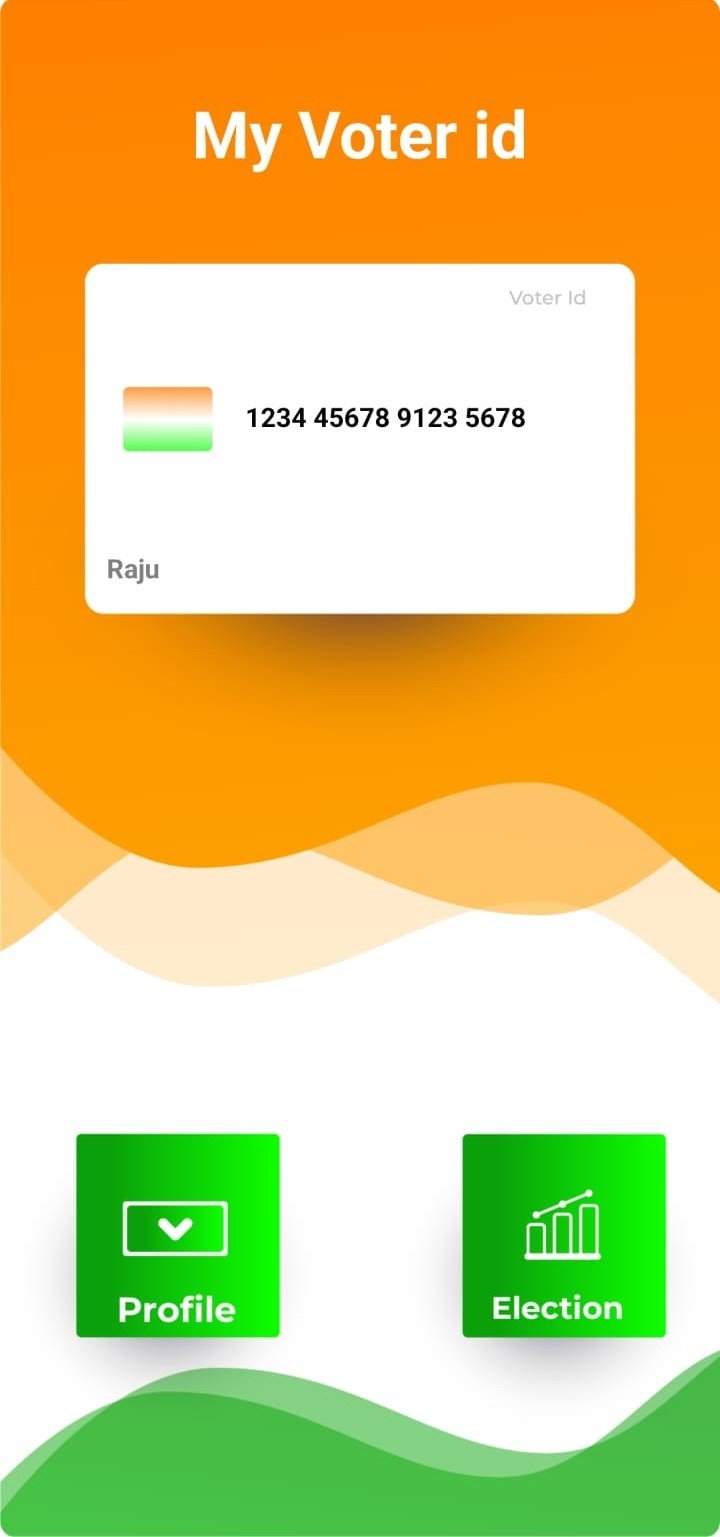
Simple Login & Registration
Easy registration and login with Voter ID and fingerprint scan.
Digital Voter Card
View and manage your digital voter card within the app.
Seamless Voting
Cast your vote with simple, secure fingerprint authentication.
Our Roadmap
Our journey to ensure full integrity and public trust.
Soft Launch
Launch for a limited public audience.
Public Testing
1-month public testing with demo elections.
Enhance
Improve based on feedback and re-test.
Full Launch
Official public launch after integrity is established.
LOCK
Bridging Physical and Digital Security for Quantum-Resistant Cyber Defense.
Abstract
Traditional cybersecurity measures such as encryption, firewalls and authentication are no longer adequate to prevent sophisticated cyber attacks, including remote hacking and social engineering. The rise of quantum computing further threatens existing security protocols, making it essential to adopt a more resilient approach. LOCK (Layered Operation Control Key) introduces a hybrid security model that integrates physical intervention with digital security, requiring manual activation via a hardware-assisted switch before executing critical operations. This ensures that unauthorized actions cannot occur remotely, effectively mitigating the risk of cyber intrusions. LOCK enhances cybersecurity by combining behavior-based threat detection, dynamic access control, attacker deception and real-time monitoring. Instead of relying on traditional virus databases, LOCK analyzes system behavior to identify anomalies and proactively blocks potential threats. Additionally, it generates decoy data to mislead attackers, reducing the likelihood of repeated breaches. By bridging the gap between physical and digital security, LOCK offers a scalable, cost-effective and adaptive solution to counteract emerging cyber threats, providing enhanced protection for individuals, enterprises and critical infrastructures.
Core Concept
LOCK is designed to bridge the gap between physical and digital security by requiring manual user intervention before executing sensitive system operations. Unlike traditional software-based solutions that depend on digital authentication alone, LOCK ensures that remote attackers cannot gain unauthorized access without physical confirmation. The system acts as an intermediary security layer, intercepting all system requests, analyzing them for legitimacy and deploying countermeasures if malicious intent is detected. LOCK's core innovation lies in its combination of physical security with intelligent cybersecurity mechanisms, ensuring that critical operations such as accessing sensitive data, modifying system settings, or executing privileged commands require both digital authentication and a manual activation step. This makes remote hacking attempts ineffective, as attackers cannot manipulate the system without direct physical access.
The Digital Framework
Proactive defense through behavior-based analysis, real-time monitoring, and deception.
Threat Detection & Response
- Behavior-Based Detection: Instead of relying on a virus database, LOCK monitors system behavior to detect suspicious activity, analyzing file types and expected behaviors.
- Real-Time Anomaly Detection: Continuously analyzes user behavior, system processes, and network activity to identify deviations from normal patterns and mitigate threats like ransomware.
- Automated Incident Response: Immediately takes defensive action by blocking suspicious activities when a threat is detected.
Attacker Deception & Decoys
- Fake Data Generation: Delivers realistic-looking but fake data when an attacker tries to access restricted files, ensuring they gain no valuable information.
- Intrusion Logging: Every interaction with decoy data is monitored and recorded, allowing security teams to trace intrusion attempts and analyze attack patterns.
- Virtual Sandboxing: Lures attackers into a controlled environment, making them believe they have accessed critical resources while they interact with dummy systems.
The Physical Framework
A hardware-assisted layer of security to prevent unauthorized remote access.
Manual Activation Switch
A physical switch that must be manually engaged before executing critical system operations, preventing remote attackers from gaining unauthorized access.
USB Security Device
Acts as an intermediary layer between the system and its security framework, ensuring only authorized users with the device can enable system access.
Secure Data Storage & LED Indicators
Stores security rules in tamper-proof memory and provides real-time visual feedback on the system's security status.
1st Place Winner
IEEE CCET Student Paper Contest 2025 - Kochi Hub
Recognized for innovation in bridging physical and digital security.
LOCK vs. The Competition
A clear-cut comparison against traditional antivirus software.
Feature Breakdown
One-Time Cost
No recurring subscription fees.
Complete Offline Protection
Works without an internet connection.
Lightweight & Fast
Minimal impact on system performance.
No Data Collection
Your data and privacy are respected.
Advanced File Type Filtering
A unique layer of proactive defense.
Read the Full Report
Dive deeper into the technical details and research behind LOCK by downloading our award-winning IEEE paper.
Download Project Report (PDF)